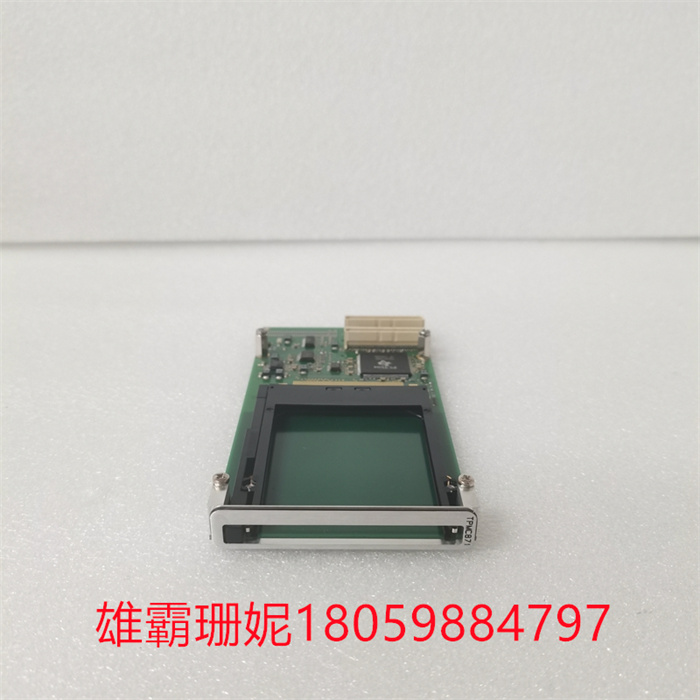
TEWS TPMC871-10 输出模块数字

系统服务器主要负责对域内系统数据的集中管理和监视,包括报警、日志、事故追忆等事件的捕捉和记录管理,并为域内其它各站的数据请求(包括实时数据、事件信息和历史记录)提供服务和为其它域的数据请求提供服务。运行系统以系统服务器为中心,完成所有功能。系统服务器还提供二次数据处理和历史数据管理和存档功能。
现场控制站是DCS系统实现数据采集和过程控制的重要站点,主要完成数据采集、工程单位变换、控制算法处理、输出控制、通过系统网络将数据和诊断结果传送到系统服务器等功能。现场控制站由主控单元、智能I/O单元、电源单元和专用机柜四部分组成,在主控单元和智能I/O单元上,分别固化了实时控制软件和I/O单元运行软件。现场控制站内部采用了分布式的结构,与系统网络相连接的是现场控制站的主控单元,可冗余配置。主控单元通过控制网络(CNET)与各个智能I/O单元实现连接。
工业公司应确保自身网络设计良好,有着防护周全的边界。企业应按ISA IEC 62443标准划分自身网络,保护所有无线应用,部署能快速排除故障的安全远程访问解决方案。公司网络,包括其工业网络基础设施设备,都应列入监视对象范围。运营技术(OT)团队可能会觉得公司的终端受到边界防火墙、专利安防软件、专业协议和物理隔离的防护,可以抵御数字攻击。但事实不是这样的,雇员、承包商和供应链员工将他们的笔记本电脑或U盘带入企业网络时,这些安全防护措施就被绕过了。必须确保所有终端都是安全的,要防止员工将自己的设备接入公司网络。事实上,黑客可以侵入OT环境中基于PC的终端。公司企业还应保护其IT终端不受OT环境中横向移动的数字攻击侵袭。
检测主电路的电压、电流等,当发生过载或过电压等异常时,为了防止逆变器和异步电动机损坏。工业世界联网程度的提升有一个关键问题:如果发生网络攻击且攻击成功,后果不堪设想,比如,网络罪犯入侵计算机系统并切断城市供电或供水。而且,不仅网络犯罪团伙会盯上ICS,民族国家黑客也常将ICS列为攻击敌对国关键基础设施的入口点。正如2017年6月NotPetya数据清除恶意软件爆发所展现的,ICS已经成为网络犯罪的主要目标。然而,很多工控设备都面临安全措施老化过时的风险,需要进行替换或升级。如何应对ICS面临网络攻击风险的事实?公共事业机构该从哪里开始防御这种之前从未考虑过的威胁?
TEWS TPMC871-10 输出模块数字

The system server is mainly responsible for the centralized management and monitoring of system data in the domain, including the capture and record management of alarms, logs, accident memories and other events, and provides services for data requests of other stations in the domain (including real-time data, event information and historical records) and for data requests of other domains. The running system takes the system server as the center and completes all functions. The system server also provides secondary data processing and historical data management and archiving functions.
The field control station is an important station for DCS system to realize data acquisition and process control, which mainly completes the functions of data acquisition, engineering unit transformation, control algorithm processing, output control, and transmitting data and diagnosis results to the system server through the system network. The field control station consists of four parts: main control unit, intelligent I/O unit, power supply unit and special cabinet. On the main control unit and intelligent I/O unit, real-time control software and I/O unit running software are solidified respectively. The field control station adopts a distributed structure, and the main control unit of the field control station is connected with the system network, which can be configured redundantly. The main control unit is connected with each intelligent I/O unit through a control network (CNET).
Industrial companies should ensure that their networks are well designed and have well-protected borders. Enterprises should divide their own networks according to ISA IEC 62443 standard, protect all wireless applications, and deploy secure remote access solutions that can quickly troubleshoot. The company network, including its industrial network infrastructure equipment, should be included in the scope of monitoring. Operational Technology (OT) teams may feel that the company's terminals are protected by border firewalls, proprietary security software, professional protocols and physical isolation, and can resist digital attacks. But this is not the case. When employees, contractors and supply chain employees bring their laptops or USB flash drives into the enterprise network, these security measures are bypassed. All terminals must be secure, and employees should be prevented from connecting their devices to the company network. In fact, hackers can invade PC-based terminals in the OT environment. Companies should also protect their IT terminals from digital attacks that move horizontally in the OT environment.
Detect the voltage and current of the main circuit, in order to prevent the inverter and asynchronous motor from being damaged when overload or overvoltage occurs. There is a key problem in improving the degree of networking in the industrial world: if a cyber attack occurs and succeeds, the consequences will be unimaginable. For example, cyber criminals invade computer systems and cut off urban power or water supply. Moreover, not only cyber criminal gangs will target ICS, but also hackers in nation-state often list ICS as the entry point to attack the key infrastructure of hostile countries. ICS has become the main target of cyber crime, as shown by the outbreak of malicious software in NotPetya data cleaning in June 2017. However, many industrial control equipment are facing the risk of outdated safety measures and need to be replaced or upgraded. How to deal with the fact that ICS faces the risk of cyber attacks? Where should public utilities start to defend against this threat that has never been considered before?